Rapid Growth Predicted for Identity Access Management (IAM)
In a nutshell, Identity and Access Management (IAM) is the security and business discipline that enables the right individuals to access the right resources at the right time, and for the right reasons.
Independent research reports that the IAM market is estimated to grow from USD 8.09 Billion in 2016 to USD 14.82 Billion by 2021, at a CAGR of 12.9% between 2016 and 2021.
The increased adoption of cloud specific services such as (SaaS) Software as a Service; (IaaS) Infrastructure as a Service; and (PaaS) Platform as a service, creates more demand for security access to corporate information. The consumerisation of IT and the increase of BYOD usage as well as the growth of IoT devices, are all fuelling a rise in cybercrime. Internet security is now top of the agenda for organisations and governments worldwide. Further, the increasing uptake of Blockchain is not surprising given its inherent security with peer-to-peer, encrypted transactional communications.
Compliance is a Key Driver
While compliance is a key driver for better information governance, with the associated impact of the latest GDPR legislation, there is also an increasing focus on risk management. Data leakage through unauthorised access can result in significant financial losses and damage to corporate brand. Recent data breeches by Cambridge Analytica and the ever-growing cyber security threats worldwide, underscore the importance of having the right Identity Access Management solutions in place.
Boss Equity predicts further consolidation via acquisition in this hot sector, as worldwide demand for Identity Access Management and associated internet security, governance, risk and compliance solutions increases.
Read the full IAM article, recently posted by John Symon, SVP International Markets at Boss Equity by clicking here.
Meanwhile, guest author and contributor, Amruta Joshi, highlights below the Top 5 Identity Access Management Trends. 
Technology keeps advancing with each passing day and it is vital to stay abreast with its rapidly changing technology trends. Digital transformation of organizations is a part of the process for the organizations and business owners who want to keep up with these trends. Along with various advantages, digitization comes with its own set of challenges. This holds even truer when it comes to identity and access management (IAM). Businesses need to take interest in planning a strong IAM strategy to secure the access and control over the devices and systems that are being used by various components of the organization.
Identity and access management or identity management is a security system that grants access to the vital resources to the right organizations. It is essential for these systems to allow this access at the right time and reason as well, which makes IAM both an asset and a liability. First and foremost, since the security definitions and formats keep changing, it is vital for the organizations to make sure their identity access management tools are not outdated or unsuitable for the advanced gadgets and functions. Hence, adopting the proper identity and access management systems becomes vital for the overall security strategy of a business.
What Does Identity and Access Management Strategy Entail?
The pace of disruptive changes is unprecedented, when it comes to identity and access management. Hence, the business leaders need to address the numerous interdependencies of diverse business platforms and ecosystems. The aim is to make the businesses agile and capable to respond to threats in real-time. Internet of things (IoT) and cloud are the primary threats when it comes to data privacy and cyber security. Hence, majority of organizations have set higher security budgets for the security of their organizations.
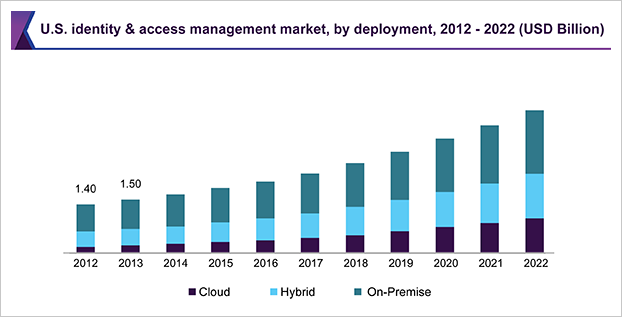
The identity management strategy primarily assists in controlling the instances of internal security threats. Most companies prefer on premise identity and access management solutions, while a large section also prefers hybrid model— combination of on premise and cloud IAM solutions.
 Hybrid solutions prove highly effective for mobile enterprise. Advancements in cloud-based Identity-as-a-Service (IDaaS) and introduction of innovative solutions from Okta and Centrify among others can change this scenario in the near future. Image source: www.grandviewresearch.com
Hybrid solutions prove highly effective for mobile enterprise. Advancements in cloud-based Identity-as-a-Service (IDaaS) and introduction of innovative solutions from Okta and Centrify among others can change this scenario in the near future. Image source: www.grandviewresearch.com
The basic role of identity and access management solutions is to associate all the activities within a business ecosystem with a device or specific user and then keep a track of those activities and report them. However, just monitoring and overall governance is not enough as the organizations require strong user authentication services like single-sign-on (SSO) for a large scale of devices or users. However, adopting the strongest on-premise, cloud or hybrid security platform is not enough because the networks, applications and devices have separate security protocols.
Hence, the primary key to successful implementation of digitization involves developing quick and easy access solutions that can be shared by business owners, partners and employees. Since organizations need to manage a diverse set of resources, only the use of diverse authentication protocols for identity and access management makes sense. With trends such as 'bring your own device' (BYOD), IoT, and connected enterprises, it is vital for the IAM strategy to be identifiable across multiple domains. This involves large investments in terms of manpower and hardware.
Top Trends in Identity and Access Management
Industries as well as governments from around the world have a lot at stake, when it comes to identity management. They need to come up with the solutions that can ensure safety for the intellectual property without wasting financial resources or causing major harm to the reputation of the organizations. As the unstructured data multiplies with the rising use of mobile platforms, the companies dealing with IAM solutions need to be prepared to address the threats and restrictions that might hinder growth and smooth operations. Here are some of the top trends observed in the global identity and access management market:
Identity Assurance
The industry has moved on from simply the use of password management solutions to provide access to the users that require the particular resources necessary for them to do the tasks. Today, decision-based identity assurance has become the predominant trend. This involves considering the context when it comes to access requests for resources from particular individuals. Identity assurance also looks for the signs and warnings for threats to internal and external IT infrastructure. It helps keeping track of suspicious activities and informs when one needs to increase the security layer or block access. In short, the aim is to develop and implement a flexible and user-friendly yet safe security authentication mechanism.
#1 Security Robotics
Robotics is increasingly becoming a vital element of various fields including agriculture, media and entertainment, and healthcare among others. In near future, the technology is anticipated to enter the enterprise settings with respect to identity and access management. While the labor intensive industries are increasingly replacing manual tasks by robotics, the security sector aims to provide the robotics with vital tasks of managing access rights and identity context. Digital identity management can be a real boon for the industries committed to innovation and implementation of security measures of the highest standards. The robotic process automation or RPA allows businesses to gain competitive edge in no time while accelerating the productivity and accuracy of all the processes.
#2 Identity API Management
This is one of the most revolutionary trends in the market for identity and access management. The identity application programming interface (API) management allows connection of cloud applications and people to give programmer-level access and audit trails to anyone trying to access API gateways. It also involves gathering information from one or more trusted sources and standardizing them. Increasing adoption of intelligence to boost interaction between applications and APIs. The Azure Portal by Microsoft or Identity Bridge by Avancer could be some of the examples of this technology. Identity API management also works in hybrid setups, offering synchronous and easy functionalities.
#3 Serverless Security
The serverless architecture or apps highly depend on backend as a service (BaaS) or various custom codes. The problem with serverless apps and their operations and management is the lack of opportunity for tracking in terms of security. Moreover, as the systems grow in scale, it becomes even more difficult to remove and replace older functions. This develops dependability of applications and vulnerable to security threats and attacks. Hence, the top players dealing with serverless architecture are keen on developing strong identity and access management solutions for serverless apps. Rising research and development in serverless apps and IAM seems to be one of the promising trends for near future.
#4 Connected and Pervasive
The modern day identity and access management involves the use of buzzwords like real-time, flexible, uninterrupted, and connected. Businesses from around the world are spending time and money in developing technologies that take care of the aforementioned aspects of identity and access management. It is essential for the modern organizations to come across an identity management tool that offers seamless and continuous authentication. Instead of a one-time event, IAM is a non-stop process that keeps finding upgrades when it comes to advanced threats and security protocols. It is vital for the identity management solutions to be inclusive enough to provide authentication to even the large enterprises and ecosystems designed with next generation firewalls.
#5 General Data Protection Regulation (GDPR)
The General Data Protection Regulation is a regulation the European Union (EU) law that deals with data privacy and protection. The GDPR is intended to unify and strengthen data security in the EU territory. The impending implementation of this regulation is anticipated to drive the U.S.-based companies to pay additional attention to data privacy and governance. The regulation is anticipated to encourage organizations to pay heed to added security of sensitive data, repositories of unstructured data, and overall usage and distribution on information across various ecosystems and processes.
How Will These Trends Fare within the IAM Market?
It is anticipated that the global identity and access management (IAM) market will witness steady growth in the forthcoming years. According to research by Grand View Research, the market is poised to reach past a valuation of around USD 24.55 billion by the year 2022, growing at a healthy CAGR. Rapid rise in the use and demand for web-based applications is considered as the primary driver for the global market. Research and development activities and adoption of stern policy-based compliance are also expected to be some of the vital factors positively influencing the global market for IAM. Preference for cost containment and audit management may play essential role in adoption of identity management across various end-use sectors.
Large scale enterprises are spending heavily on identity and access management solutions. Rising awareness regarding advanced threats and availability of security solutions can further propel the demand for IAM solutions in near future. Governments from around the world have increased the stringency of compliance framework for the SMBs as well as large enterprises. This is anticipated to drive the demand for advanced solutions in the years to come. Technological advancements and adoption of automated business processes, especially across emerging economies can drive the market in the years to come. For instance, adoption of the trends like BYOD, IoT, connected device, and other technologies is expected to drive the need for identity and access management.
The government of United States of America has issued around 400 regulatory guidelines for cyber security. Adherence to these policies is a priority for the companies operating in the market. This factor is expected to propel growth in demand for identity and access management across the region. Many federal agencies require their employees to make use of personal identification verification cards and other modern authentication alternatives. This is even more important when it comes to using the government IT infrastructure and networks. This stringency can drive the market for identity and access management over the next few years to come.
How are the Top Market Players Dealing with IAM?
Some of the top IAM market players including IBM, HID Global Corporation, Dell Software, HP, OneLogin, Oracle, and Amazon Web Services among others are inclined towards technological advancements and R&D. Mergers and acquisitions (M&A) and business collaborations are also some of the primary strategies observed in the global identity and access management market. To put this into perspective, IBM recently acquired CrossIdeas.
Widespread adoption of mobile devices and cloud services is a boon as well as bane for the companies. Despite aggressive competition, the top vendors in this market are in vulnerable positions due to the changing security parameters, advancing technologies, and evolving requirements from a vast customer base from around the world. Hence, it becomes crucial for the market leaders to keep an eye on the changing trends in the market and develop innovative tools and solutions to deal with the changing requirements.
As far as business expansions are concerned, some of the leading players in the identity and access management market are looking for investment opportunities across emerging markets. Currently, North America is the leading region in terms of revenue as well as the overall market share thanks to the positive regulatory scenario.
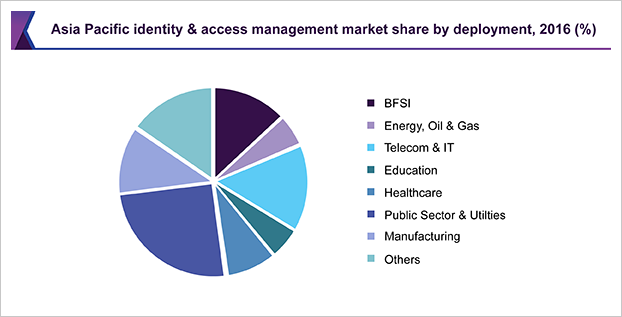
 However, in the near future, Asia Pacific is expected to emerge as the fastest growing region. High deployment of identity and access management solutions and growth in cyber threats and cyberattacks can propel the region at a steady pace.
However, in the near future, Asia Pacific is expected to emerge as the fastest growing region. High deployment of identity and access management solutions and growth in cyber threats and cyberattacks can propel the region at a steady pace.
Image source: www.grandviewresearch.com
The organizations operating in the global identity and access management market need to find ways to break away from legacy manual processes. According to the experts, cloud-based identity governance and administration (IGA) is unavoidable. Hence, it is vital for the companies to embrace a rational approach to access risk management so they can provide end-users with a user-friendly business experience.
Author Bio:
Amruta Joshi is a Content Writer specializing in varied industry verticals including personal care, healthcare, chemical and technology. Her work includes market research and writing blogs, PRs, guest posts, etc. on all the latest innovations and up to date events of her field. She has also done freelancing for an IT & software firm and has also worked as a full-time Copy Editor for a renowned German publisher for STM books.
https://www.linkedin.com/company/grand-view-research/
info-apac@grandviewresearch.com
https://www.grandviewresearch.com/