By John Symon, SVP, International Markets
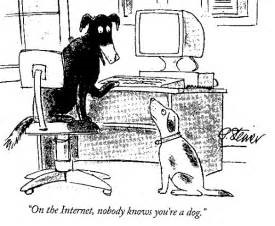
Many of you will remember the iconic cartoon below by Peter Steiner, published in the New Yorker magazine in 1993, highlighting the anonymity and liberating access for all in the early days of the internet.
In the ensuing two decades the internet has transformed the daily lives of individuals, businesses and governmental organisations. With the advancement of Web 2.0 factors such as social, mobile, Cloud and data analytic technologies, internet access, security and information governance have become key boardroom issues to manage risk and compliance and to combat the ever-increasing spectre of data leakage and cybercrime.
What is Identity Access Management and Why Does it Matter?
Identity and Access management (IAM) is the security and business discipline that enables the right individuals to access the right resources at the right time, and for the right reasons.
Identity and Access Management ties dissimilar applications together into a single source for management of access and entitlements. IAM solutions will often provide access management workflows, user entitlement reporting, application owner entitlement reviews, and even single-sign-on (SSO) functionality between applications with the goal of providing a single entitlement store and workflow solution for, and controlling, access management.
What makes IAM so critical is that access rights, typically accumulate over a time. The longer a user stays with a company, the more access the user usually has. Users with privileges beyond what is required to perform in their current role can put the company at risk. Moreover, if a hacker gains access to the account of a user with excessive access, it might further increase the company’s risk. Both scenarios can result in a data breach and financial loss.
When it comes to areas such as usernames and passwords, everyone is asked to input their login details everyday with multiple log-in combinations be it for work email, personal email, business applications and content repositories. The same applies for social media platforms such as Facebook and Twitter, as well as e-commerce accounts such as Amazon and Online Banking, not to mention accessing corporate CRM systems etc. This makes API management crucial with App2App passwords everywhere.
Whether a publicly traded corporation, a government institution, a small to medium-sized business, or even a start-up, organisations need to ensure they are compliant with identity access solutions. Given the regulatory, security, and PR implications, the need for IAM solutions has never been greater and may be the single most important solution that needs to be deployed.
As of 2017, the average professional is likely to be keeping track of dozens of username/password combinations. While the process seems to work well enough, it is in fact remarkably old, unreliable, insecure, and worst of all, insecure while not meeting regulatory compliance requirements.
Another aspect is the blurring lines between the world we live in and the one where we work. The surplus of mobile devices in the workplace, Cloud computing and new corporate policies allowing employees to access secure corporate networks with their own phone or tablet complicate things further.
Added to that, the advancement of Cloud computing and the evolutions of distributed systems, data and networks, you’ve got a flood of security challenges for IT professionals to protect the key corporate information and data assets.
IAM Now Part of Identity Governance & Administration (IGA) Market
As stated by Gartner “the Identity and Access Management market has experienced significant upheaval along with its usual growth over the past two years. What began as two relatively distinct markets, user provisioning and access governance, have merged into a single category of identity governance and administration.
Identity Governance and Administration (IGA) is a set of processes to manage identity and access information across systems. It includes management of the identity life cycle that creates, maintains and retires identities as needed, as well as governing the access request process, including approval, certification, risk scoring and segregation of duties (SOD) enforcement.
Core functionality includes identity life cycle processes, automated provisioning of accounts among heterogeneous systems, access requests (including self-service) and governance over user access to critical systems via workflows for policy enforcement, as well as for access certification processes. Additional capabilities often included in IGA systems are role management, role and entitlements mining, identity analytics, and reporting”.
The Impact of Big Data & Growth of Unstructured Information
Organisations need to process more and more unstructured data, such as documents, spreadsheets, presentations or e-mails, daily. This leads to greater challenges in establishing the right file and access authorisation systems.
Information security is threatened by unauthorised and undesired access rights held by both current and previous employees. Further, with the wider usage of EFSS (Electronic File Synch & Share) systems deployed by companies such as Box, Dropbox and many others, including MS Office 365 and OneDrive, identity access management has become a critical component in protecting corporate information assets.
What is now required is clarity on who may access what data, who controls access to such data and whether the file system has any structural weaknesses that might facilitate unwanted data leakage. This requires well-structured access management in addition to common identity access management solutions. It also increasingly needs to be a core component of any ECM or Information Management system.
The Cloud Puts Organisations at Greater Risk
Enterprises now use an average of 1,031 cloud apps, a figure that IT often underestimates by 10x and which represents just one of many avenues that hackers could breach to obtain sensitive data.
There were a reported record 1093 data breaches in 2016, with 37 million records compromised at an average cost of $221 per stolen record and a cost of some $7 million per breach.
According to the Identity Theft Resource Center, ‘U.S. companies suffered a record 1,093 data breaches last year, a 40 percent increase from 2015. Headline-grabbing hacks, with victims ranging from Wendy’s Co., the Panama Papers, to the Democratic National Committee and Dropbox password leaks, are increasing, despite regulatory scrutiny and more aggressive cyber-security spending’.
Forrester estimates that 80% of all data breaches involve the misuse of administrative privileges.
Cybersecurity – Fuels Further Growth for IAM Solutions
IAM solutions also address the broader Cybersecurity market. The increased adoption of Cloud computing across various end user industries is propelling growth in the global cloud security market. Various types of cloud security services include identity and access management, web security, email security and data loss prevention have accelerated demand for cloud security solutions. Further, the application of behavioural analysis and network forensics are increasingly required to detect cyberattacks.
The increased adoption of cloud specific services such as (SaaS) Software as a Service; (IaaS) Infrastructure as a Service; and (PaaS) Platform as a service, places more demand for security access to corporate information. Further, with the consumerisation of IT and the increase of BYOD usage and growth of IOT devices this is fuelling a rise of cybercrime. Internet security is now top of the agenda for organisations and governments worldwide.
According to research by Cybersecurity Ventures, the level of spending on cyber security solutions is reaching unprecedented levels in both the private and public sectors. Spending is expected to increase from $75.4 billion in 2015 to $170 billion in 2020.
While compliance is a key driver for better information governance, there is an increasing focus on risk management. Data leakage through unauthorised access can result in significant financial losses and damage to corporate brand.
Rapid Growth & Further Consolidation Expected for the IAM Market
Independent research from MarketsandMarkets reports that the identity and access management market is estimated to grow from USD 8.09 Billion in 2016 to USD 14.82 Billion by 2021, at a CAGR of 12.9% between 2016 and 2021.
Stringent regulations for numerous industries such as financial services, pharmaceutical, healthcare and other highly regulated industries necessitate the establishment of secure access control infrastructure facilities. Strict government regulations and several regulatory reforms are causing organisations as well as enterprises to address their internal control infrastructure.
Solutions Review identifies some 28 leading vendors offering specific IAM solutions. However, there are many more companies providing key elements of identity access management in areas such as SSO (Single Sign On), Privileged Account Management, two factor authentication as well as the broader internet and cybercrime security market.
According to Gartner, “The Identity Governance and Administration (IGA) market is maturing into an early mainstream phase. IAM and security leaders should take note of emerging requirements around more risk-aware identity approaches and cloud adoption that are causing innovative vendors to integrate analytics with adjacent IT and data security technologies”.
IAM solutions should also be a major consideration for vendors providing business process, records and information management solutions that address key governance, risk and compliance issues for the secure management of both structured and unstructured information.
Detecting the Dog Before it Bites - I AM Who I Say I AM
The increased demand for identity access is highlighted by a more recent and very apt cartoon by Kaamran Hafeez, also published in the New Yorker in 2015, which underlines how identity access control has had to change and adapt to an increasingly mobile and internet connected world.

Boss Equity predicts further consolidation via acquisition in this hot sector, as worldwide demand for identity access management and associated internet security, governance, risk and compliance solutions increases.
Reference sources include:
• Solutions Review – 2017 Identity Management Buyer’s Guide
• Identity and Access Management Beyond compliance – Ernst & Young
• Kuppinger Cole Leadership Compass – Identity Provisioning
• Gartner –Magic Quadrant for Identity Governance and Administration
• Forrester Research